|
|
|


Whistleblower outs NSA's secret spy room at AT&T
Posted on April 08, 2006
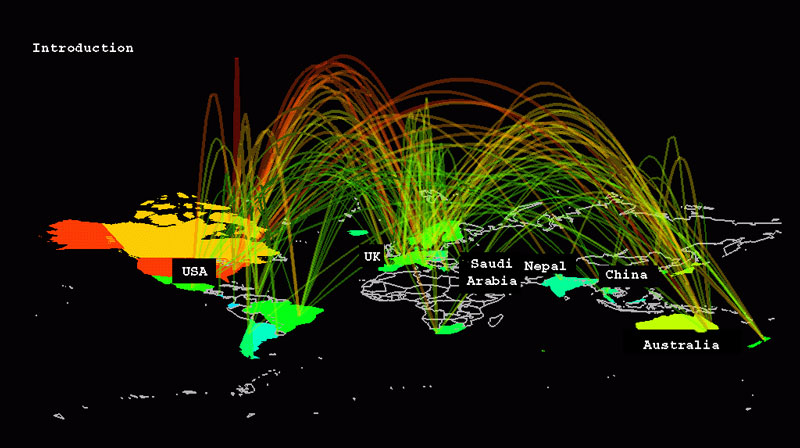
Mark Klein, a retired AT&T communications technician, said the company shunted all Internet traffic--including traffic from peering links connecting to other Internet backbone providers-- to semantic traffic analyzers, installed in a secret room inside the AT&T central office on Folsom Street in San Francisco. Similar rooms were built in Seattle, San Jose, Los Angeles and San Diego.
"Based on my understanding of the connections and equipment at issue, it appears the NSA (National Security Agency) is capable of conducting what amounts to vacuum-cleaner surveillance of all the data crossing the Internet," Klein said. "This potential spying appears to be applied wholesale to all sorts of Internet communications of countless citizens."
In 2003, the National Security Agency set up a secret room inside the phone company's San Francisco office building that was not accessible to AT&T technicians, Klein said.
The former employee's statement, as well as several documents saved by him after he left the company in 2004, shows further evidence of domestic spying initiatives by the federal government.
Klein's statement is being incorporated into a class action filed in San Francisco federal court, in which lawyers with the Electronic Frontier Foundation (EFF), Lerach Coughlin Stoia Geller Rudman & Robbins, and Traber & Voorhees in Pasadena claim that AT&T illegally allowed the NSA taps.
"Despite what we are hearing, and considering the public track record of this administration, I simply do not believe their claims that the NSA's spying program is really limited to foreign communications or is otherwise consistent with the NSA's charter or with FISA [the Foreign Intelligence Surveillance Act]," Klein said.
News that the NSA was working with major telecommunications companies first surfaced shortly before Christmas. The Bush administration has acknowledged the existence of a domestic spying program, but claims the executive order was limited to those individuals with known terrorist ties.
The Electronic Frontier Foundation filed a class-action lawsuit against AT&T on January 31, 2006, accusing the telecom giant of violating the law and the privacy of its customers by collaborating with the National Security Agency in its massive program to wiretap and data-mine Americans' communications.
"The evidence that we are filing supports our claim that AT&T is diverting Internet traffic into the hands of the NSA wholesale, in violation of federal wiretapping laws and the Fourth Amendment," EFF Staff Attorney Kevin Bankston said in a statement.
NarusInsight Intercept Suite - Packet-level, flow-level, and application-level usage information is captured and analyzed as well as raw user session packets for forensic analysis, surveillance or in satisfying regulatory compliance for lawful intercept. The capabilities include playback of streaming media (i.e. VoIP), rendering of Web pages, examination of e-mail and the ability to analyze the payload/attachments of e-mail or file transfer protocols. (source: Narus.com)
On Wednesday, the EFF asked the court to issue an injunction prohibiting AT&T from continuing the alleged wiretapping, and filed a number of documents under seal, including three AT&T documents that purportedly explain how the wiretapping system works.
After asking for a preview copy of the documents last week, the government did not object to the EFF filing the paper under seal, although the EFF asked the court Wednesday to make the documents public.
One of the documents is titled "Study Group 3, LGX/Splitter Wiring, San Francisco," and is dated 2002. The others are allegedly a design document instructing technicians how to wire up the taps, and a document that lists the equipment installed in the secret room.
The list includes a Narus STA 6400, which is a semantic traffic analyzer. The Narus STA technology is known to be used particularly by government intelligence agencies because of its ability to sift through large amounts of data looking for preprogrammed targets.
The NarusInsight Discover Suite (NDS) captures and classifies traffic and data on monitored links in real time at true carrier speeds (up to 10G/OC-192). Detailed layer 3 to layer 7 data are collected and correlated across every link and element on the network. NDS empowers users to manage IP traffic and applications including VoIP, Skype, P2P (e.g., BitTorrent, e-Donkey/e-Mule, FastTrack/Kazaa, Gnutella, etc.), messaging (AOL IM/ICQ, Yahoo IM, MSN Messenger, Jabber, IRC, MMS), streaming media (RTP, RTCP, RTSP), e-mail (SMTP,POP3,IMAP), Web browsing and push to talk (PTT). (source: Narus)
In a letter to the EFF, AT&T objected to the filing of the documents, arguing that they contain sensitive trade secrets, Wired magazine reports.
According to court rules, AT&T has until Thursday to file a motion to keep the documents sealed. The government could also step in to the case and request that the documents not be made public, or even that the entire lawsuit be barred under the seldom-used State Secrets Privilege, says Wired.
AT&T Corp. (which was recently acquired by the new AT&T, Inc,. formerly known as SBC Communications) maintains domestic telecommunications facilities over which millions of Americans' telephone and Internet communications pass every day. It also manages some of the largest databases in the world, containing records of most or all communications made through its myriad telecommunications services.